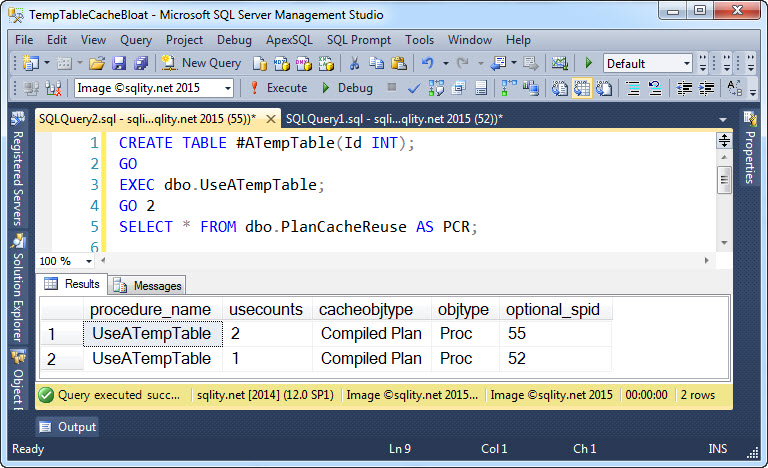
Can A Temp Table Name Cause Plan Cache Bloat?
-
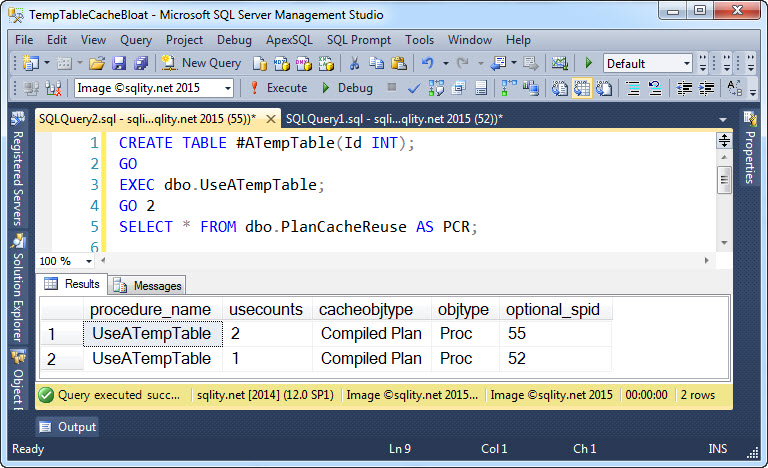
Can A Temp Table Name Cause Plan Cache Bloat?
POSTED: 2016-01-19
“Use descriptive object names.” – Read on to discover how ignoring this best practice can cause plan cache bloat and in turn performance issues.
-
Invite for #tsql2sday #71 – SQL Server Audit
POSTED: 2015-09-01
T-SQL Tuesday is a monthly blog party. This month is the 70th episode and the topic is: “SQL Server Audit”. Read on to discover what #tsql2sday is all about and what you have to do to participate in this exciting blog-party.
-

The Hidden SQL Server Gem: UPDATE from SELECT
POSTED: 2015-08-19
Sometimes we need to update data in one table based on the contents of one or more other tables. Discover how the UPDATE from SELECT variation of SQL Server’s UPDATE statement provides an easy way to achieve this.
-
2015-04-28: SQL Server Cryptology – A Primer – PSSUG SJ Meeting
POSTED: 2015-04-28
I am presenting “SQL Server Cryptology – A Primer” on April/28/2015 17:30 at the PSSUG SJ Meeting. Title SQL Server Cryptology – A Primer (Click for Abstract.) When April/28/2015 at 17:30 Where PSSUG SJ Meeting April 2015 Haddon Heights Public [more…]
-
2015-04-03: Securing Multi-Database Applications – SSWUG VC15
POSTED: 2015-03-31
I am presenting “Securing Multi-Database Applications” on April/03/2015 16:00 at the SSWUG Virtual Conference 2015. Title Securing Multi-Database Applications (Click for Abstract.) When April/03/2015 at 16:00 Where SSWUG Virtual Conference 2015
-
2015-04-02: SQL Server Cryptology – A Primer – SSWUG VC15
POSTED: 2015-03-31
I am presenting “SQL Server Cryptology – A Primer” on April/02/2015 13:30 at the SSWUG Virtual Conference 2015. Title SQL Server Cryptology – A Primer (Click for Abstract.) When April/02/2015 at 13:30 Where SSWUG Virtual Conference 2015
-
Presentation Materials: SQL Server Cryptology – A Primer
POSTED: 2015-03-31
Abstract So, you got told you need to encrypt “the database”. Now what? There are many reasons to encrypt your database. You might have to comply with HIPAA or PCI DSS, or you might just have generally sensitive data. Correctly [more…]
-
PCI DSS Compliance – Is It For Me?
POSTED: 2015-03-28
If you have a small or medium sized business, you might be wondering of your business needs to be PCI DSS compliant. Read on to find out now.
-
2015-03-21: SQL Server Cryptology – A Primer – Philly.NET Code Camp 2015.1
POSTED: 2015-03-20
I am presenting “SQL Server Cryptology – A Primer” on March/21/2015 13:30 at Philly.NET Code Camp 2015.1. Title SQL Server Cryptology – A Primer (Click for Abstract.) When March/21/2015 at 13:30 Where Philly.NET Code Camp 2015.1 Microsoft Corporation 45 Liberty [more…]
-

You’ve been Hacked! [T-SQL Tuesday #63 – Security]
POSTED: 2015-02-10
One Billion – The number of accounts affected by security breaches during the last ten years. Is the data of your customers safe with you?











