Tag: symmetric key
-
Debunking Symmetric Key Recreate-Ability
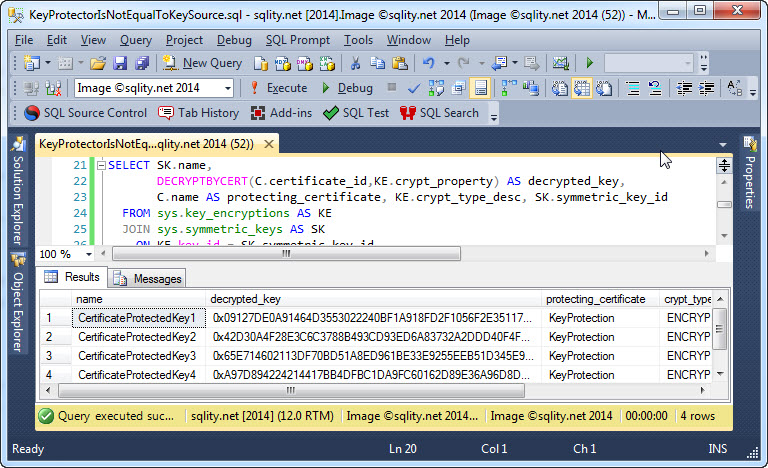
Do you think you can recreate a symmetric key that is protected by a certificate, by just using that same certificate? You might be in for a big surprise…
-
How to Crack the Symmetric Keys in the Database Wide Open
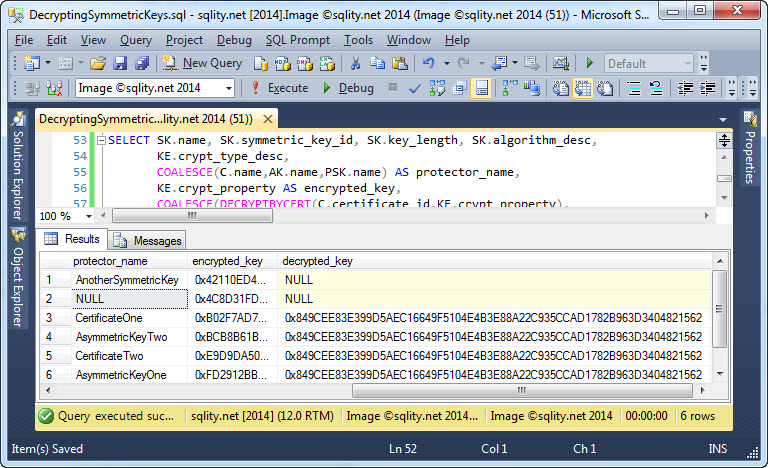
Did you always want to get to the root of symmetric key encryption in SQL Server and actually decrypt a protected symmetric key? In some circumstances this can actually be done. Find out how to do this now.
-
OPEN SYMMETRIC KEY – Avoid the NULL Ciphertext Trap
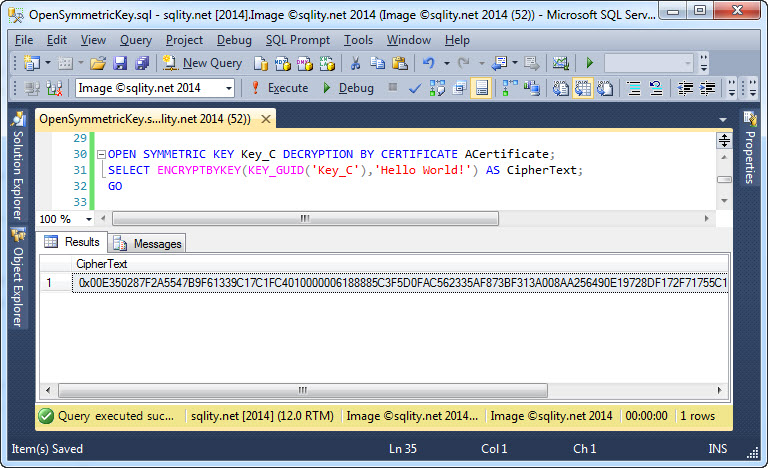
Don’t get caught in this nasty trap that will cause all your encrypted data to be wiped out. Discover how to use the OPEN SYMMETRIC KEY statement correctly to protect yourself (and your data) from this ugly surprise.
-
The sys.key_encryptions Catalog View
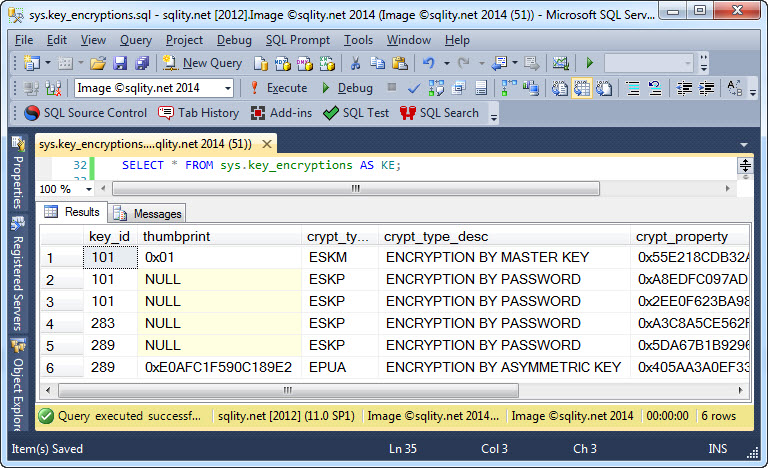
Do you have a symmetric key in a SQL Server database but forgot how it is encrypted? Discover how you can use the sys.key_encryptions catalog view to find out which protection mechanisms were used to encrypt the symmetric keys in the current database.
-
The sys.symmetric_keys Catalog View
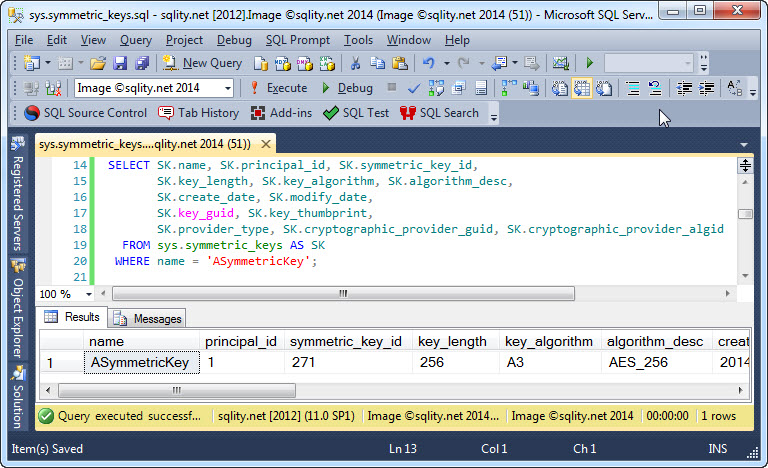
Where do you turn if you need information about the symmetric keys in the current database? Meet the sys.symmetric_keys catalog view and discover what types of information on symmetric keys it can provide.












